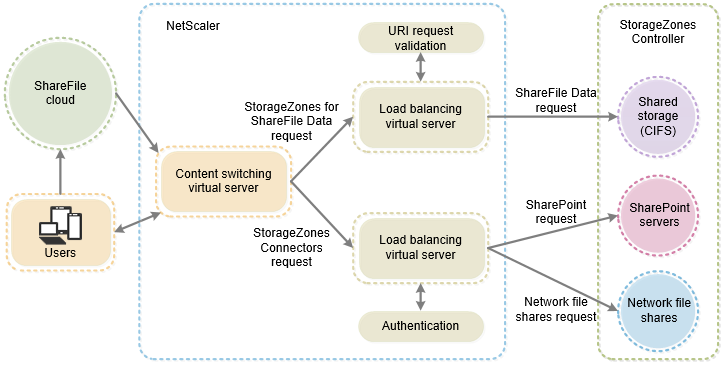
To help you set up NetScaler for ShareFile with on-premises storage zone controllers, an easy-to-use wizard is included in the GUI. The wizard prompts you for basic information about your StorageZones Controller environment and then generates a configuration that:
- Load balances traffic across StorageZones Controllers
- Provides user authentication for StorageZone Connectors
- Validates URI signatures for ShareFile uploads and downloads
- Terminates SSL connections at the NetScaler appliance
The diagram (courtesy of © Citrix Systems) shows these Netscaler components created by the configuration:
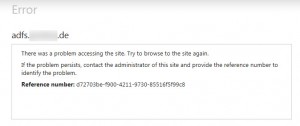
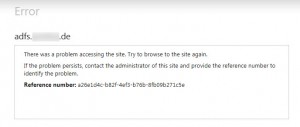
After running the built-in Setup Citrix ADC for ShareFile wizard, users starting complaining that they cannot access their network shares anymore. Those network shares have been provided via the integrated ShareFile Connector’s funcionality and has been up and running very smoothly prior to adding Netscaler to the equation.
As soon as users tried to access a network share via a StorageZone Connector they received an error indicating “Failed to load folder -The folder you are looking for could not be found”:
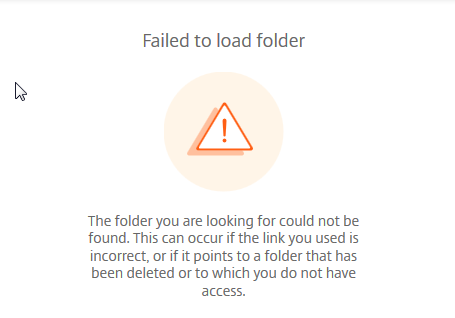
As per Citrix, you may see following error while accessing Network Shares on ShareFile Web App:
The folder you are looking for could not be found. This can occur if the link you used is incorrect, or if it points to a folder that has been deleted or to which you do not have access.
Mind that this happened with the ShareFile Web App only while accessing network shares, i.e. using within a browser, whereas accessing the exact same network share via Citrix Files for iOS worked like a charm. After having consulted our change management documentation, it quickly became clear that only one culprit could remain, as there has been no change in user passwords, permissions, group memberships, UNC paths regarding the underlying network shares, et al. All users have required permissions. The root cause could only be traced back to the changes in the Netscaler configuration a couple of days earlier. So I started investigating the details of the Setup Citrix ADC for ShareFile wizard, its configuration changes and effects on my setup by reading ShareFile On-prem and NetScaler: A Comprehensive Configuration Guide & Deep Dive, amongst others:
With having a better understanding of all things Netscaler & Sharefile, I did a little research and found a Citrix Discussion dealing with my issue and it turned out that the Setup Citrix ADC for ShareFile wizard (to the contrary) does not handle all the configuration required to access network shares via a StorageZone connector. Further configuration as to be done manually to make it work (again), as can be read here:
To support restricted zones or web access to StorageZone Connectors, you must perform additional NetScaler configuration after you complete the NetScaler for ShareFile wizard.
The additional configuration provides the Netscaler components shown in the following diagram:
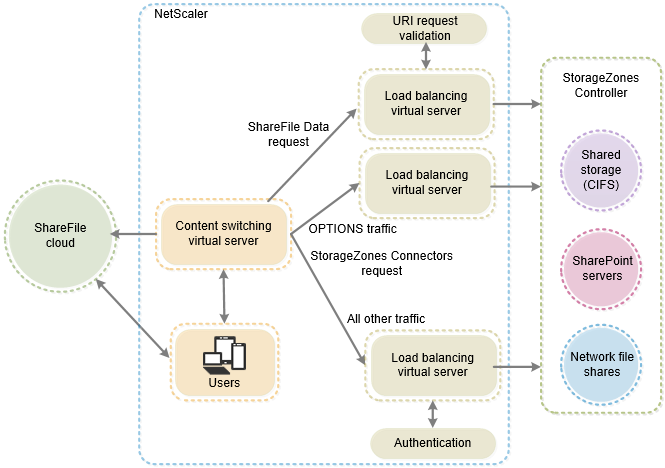
The description of the additional configuration of Netscaler in Citrix Docs is – to say the least – not very accurate. Without appropriate formatting of the corresponding text passages and additional depictions illustrating every single configuration step, manual adjustments are difficult to comprehend for non-Netscaler-aficionados. Therefore I’d like to expand on Citrix Docs and provide a more elaborate description of the configuration steps required. So, what do we need to add to the existing Netscaler configuration:
- a third NetScaler load-balancing virtual server
- a third CS policy to allow anonymous access from clients for the HTTP OPTIONS verb
- update the existing CS policy used for traffic to StorageZone Connectors (by default: _SF_CIF_SP_CSPOL)
- update the existing CS policy used for traffic to StorageZones for ShareFile Data (by default: _SF_SZ_CSPOL)
- create a heartbeat monitor for the StorageZones Controller service and bind it to the CS virtual server for ShareFile
- verify the ShareFile Load Balancing configuration
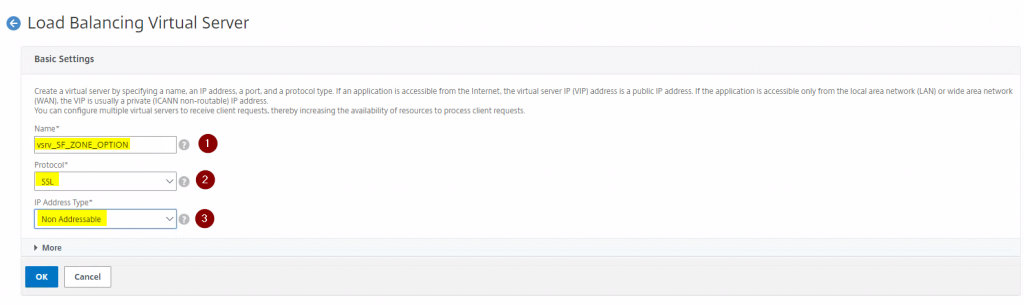
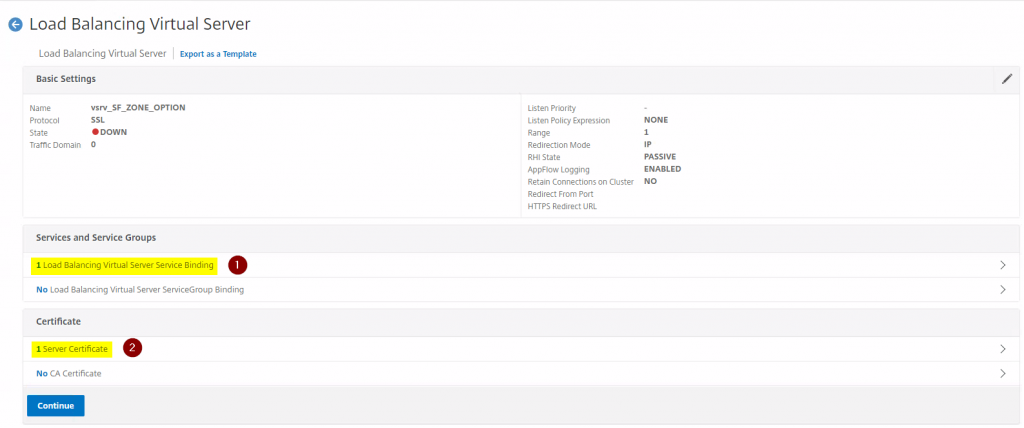
First, add a new Load Balancing vServer as follows:
add lb vserver vsrv_SF_ZONE_OPTION SSL 0.0.0.0 0 -persistenceType NONE -cltTimeout 180 bind lb vserver vsrv_SF_ZONE_OPTIONset ssl vserver vsrv_SF_ZONE_OPTION -sslProfile ns_default_ssl_profile_frontend bind ssl vserver vsrv_SF_ZONE_OPTION -certkeyName add cs policy _SF_ZONE_OPTIONS_CSPOL -rule "HTTP.REQ.METHOD.EQ(\"OPTIONS\")"
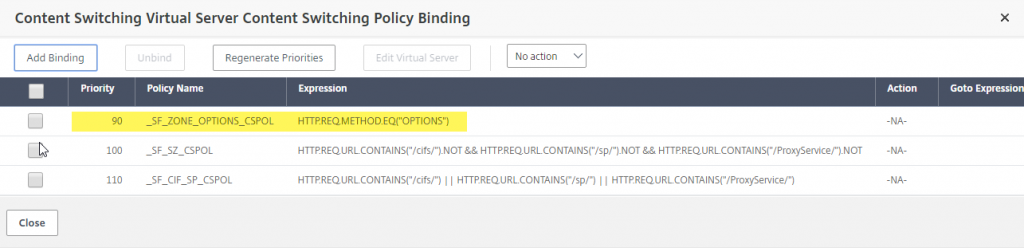
The full policy expression for the newly created CS policy (by default: _SF_ZONE_OPTIONS_CSPOL) should be as follows:
HTTP.REQ.METHOD.EQ("OPTIONS")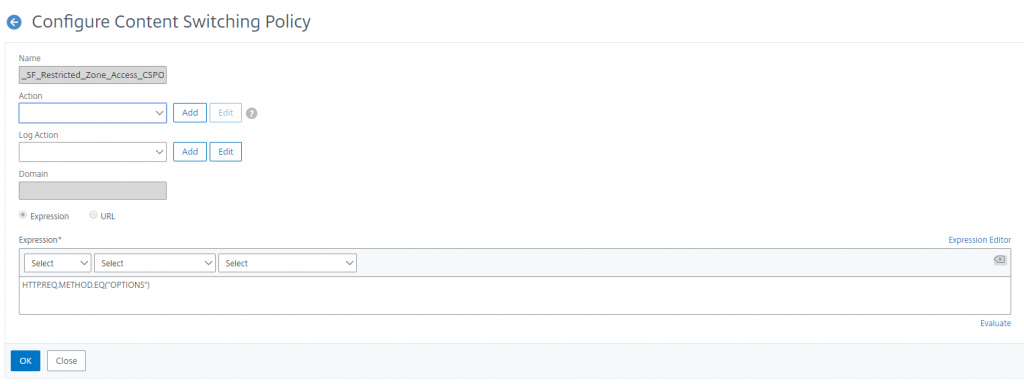
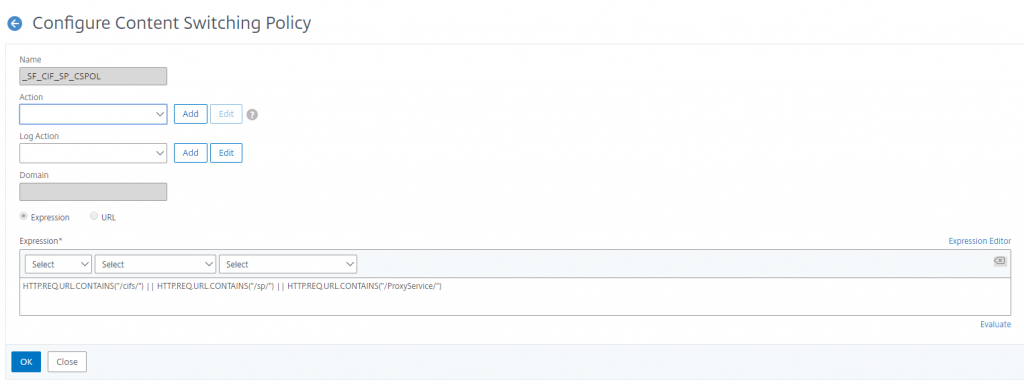
Adjust the existing _SF_CIF_SP_CSPOL policy in terms of Expression. The full policy expression for an existing _SF_CIF_SP_CSPOL should be as follows:
HTTP.REQ.URL.CONTAINS("/cifs/") || HTTP.REQ.URL.CONTAINS("/sp/") || HTTP.REQ.URL.CONTAINS("/ProxyService/")
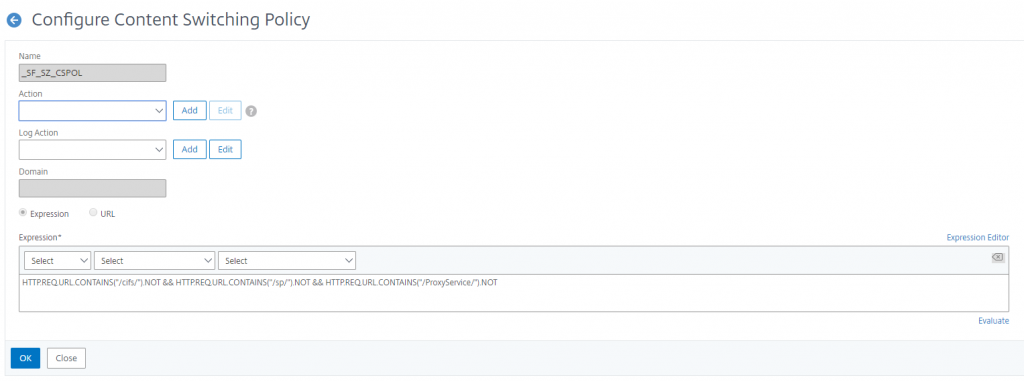
Adjust the existing _SF_SZ_CSPOL policy in terms of Expression. The full policy expression for an existing _SF_SZ_CSPOL should be as follows:
HTTP.REQ.URL.CONTAINS("/cifs/").NOT && HTTP.REQ.URL.CONTAINS("/sp/“).NOT && HTTP.REQ.URL.CONTAINS("/ProxyService/").NOT
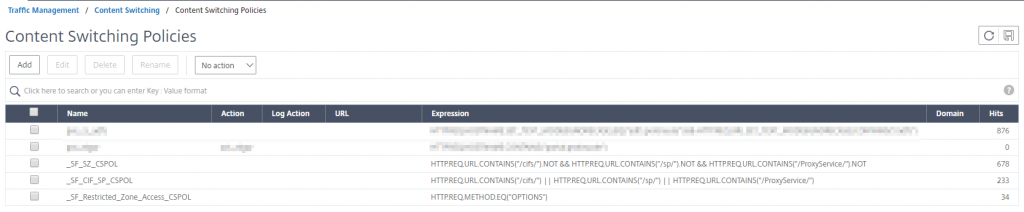
In the end your CS policies should look like this (in terms of Expressions):
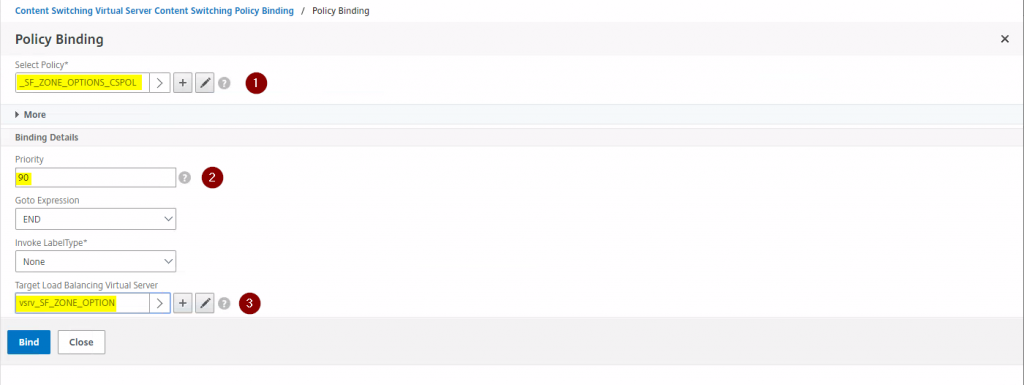
Now adjust the existing CS vServer for Sharefile (in my case vsrv_SF_CS_ShareFile) regarding its Policy Bindings in that you add the newly created CS Policy (in my case _SF_ZONE_OPTIONS_CSPOL) as the third CS policy with a Priority of 90 and set the Target Load Balancing Virtual Server to the newly created LB vServer (in my case vsrv_SF_ZONE_OPTION):
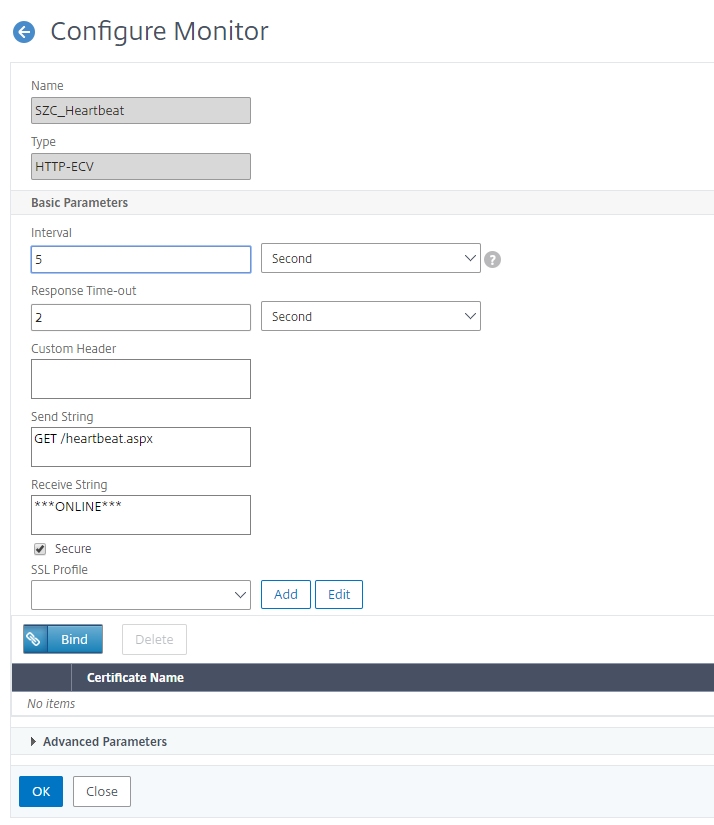
The StorageZone Hearbeat Monitor can be added using CLI by running the following commands:
add lb monitor SZC_Heartbeat HTTP-ECV -send "GET /heartbeat.aspx" -recv "***ONLINE***” -secure YES
bind service <Name of your LB service i.e. internal SF server> -monitorName SZC_HeartbeatThe newly added StorageZone Heartbeat Monitor should look as follows:
The complete CLI command list would look like this, whereas the following values need replacement according to your environment:
- CertDisplayName (server certificate name you want to bind to your vServer)
- NameOfYourSFServer (i.e. the Sharefile Server you’ve added to your NetScaler configuration)
- NameOfYourSFCSvServer (i.e. the Sharefile Content Switching vServer)
add lb vserver vsrv_SF_ZONE_OPTION SSL 0.0.0.0 0 -persistenceType NONE -cltTimeout 180 bind lb vserver vsrv_SF_ZONE_OPTIONset ssl vserver vsrv_SF_ZONE_OPTION -sslProfile ns_default_ssl_profile_frontend bind ssl vserver vsrv_SF_ZONE_OPTION -certkeyName add cs policy _SF_ZONE_OPTIONS_CSPOL -rule "HTTP.REQ.METHOD.EQ(\"OPTIONS\")" add cs policy _SF_SZ_CSPOL -rule "HTTP.REQ.URL.CONTAINS(\"/cifs/\").NOT && HTTP.REQ.URL.CONTAINS(\"/sp/\").NOT && HTTP.REQ.URL.CONTAINS(\"/ProxyService/\").NOT" add cs policy _SF_CIF_SP_CSPOL -rule "HTTP.REQ.URL.CONTAINS(\"/cifs/\") || HTTP.REQ.URL.CONTAINS(\"/sp/\") || HTTP.REQ.URL.CONTAINS(\"/ProxyService/\")" bind cs vserver -policyName _SF_ZONE_OPTIONS_CSPOL -targetLBVserver vsrv_SF_ZONE_OPTION -priority 90
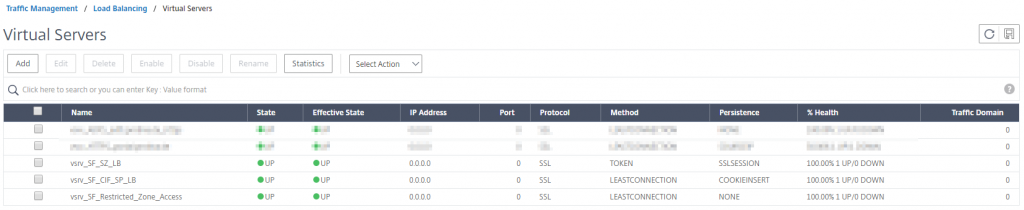
Finally, go to Traffic Management > Load Balancing > Virtual Servers to view the status of the load balancing virtual servers created for ShareFile. It may look similar to my configuration:
While testing your new configuration and accessing network shares via ShareFile connectors you should see an increasing hit number in the Hits column of your corresponding CS policies:

Update
You have to consider network restrictions as well, as Security can mess with ShareFile traffic and network flow, especially when Firewall settings do not allow corresponding (read: whitelisted) traffic to ShareFile domains, endpoints, and IPs, i.e. the ShareFile Control Plane IP ranges. Have a look at CTX208318 and CTX234446.
In another case, if you attempt to access the ShareFile network share and it prompts for users credentials, the ShareFile Web App credentials may not work. Have a look at CTX233739 as well:
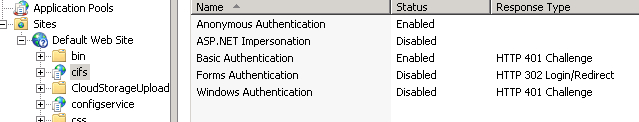
Solution
Authentication settings of an IIS CIFS server on StorageZone Controller needs correction. Please follow the steps to resolve the issue:1. Log onto the StorageZone Controller(s) and open IIS.
2. Expand Default web site
3. Click on the CIFS virtual directory, then on Authentication.
4. Ensure Anonymous is Enabled
5. ASP .NET Impersonation is Disabled
6. Basic Authentication is Enabled
7. Forms Authentication is Disabled
8. Windows Authentication is DisabledReference: The Authentication settings of an IIS CIFS server
Further reading:
- Citrix Blogs – ShareFile On-prem and NetScaler: A Comprehensive Configuration Guide & Deep Dive:
https://www.citrix.com/blogs/2018/07/24/sharefile-on-prem-and-netscaler-a-comprehensive-configuration-guide-deep-dive/ - Citrix Docs – Configure NetScaler for StorageZones Controller:
https://docs.citrix.com/en-us/storagezones-controller/5-0/install/configure-netscaler.html#sf-deploy-cfg-netscaler-wizard-extra-cfg - Citrix Discussions – Restricted zone setup: Failed to load folder:
https://discussions.citrix.com/topic/390096-failed-to-load-folder/ - Citrix Discussions – Failed to load folder:
https://discussions.citrix.com/topic/390096-failed-to-load-folder/ - CTX208318 – ShareFile Firewall Configuration – Domains and FTP information to whitelist:
https://support.citrix.com/article/CTX208318 - CTX234446 – ShareFile Firewall Configuration – IP addresses to whitelist:
https://support.citrix.com/article/CTX234446 - CTX114999 – Troubleshooting Authentication Issues Through NetScaler or NetScaler Gateway with aaad.debug Module:
https://support.citrix.com/article/CTX114999 - CITRIX SHAREFILE STORAGE ZONES, NETSCALER UNIFIED GATEWAY AND ADFS (for terms of a better understanding):
https://bretty.me.uk/citrix-sharefile-storage-zones-netscaler-unified-gateway-and-adfs/